/
Detection without response is theatre
/
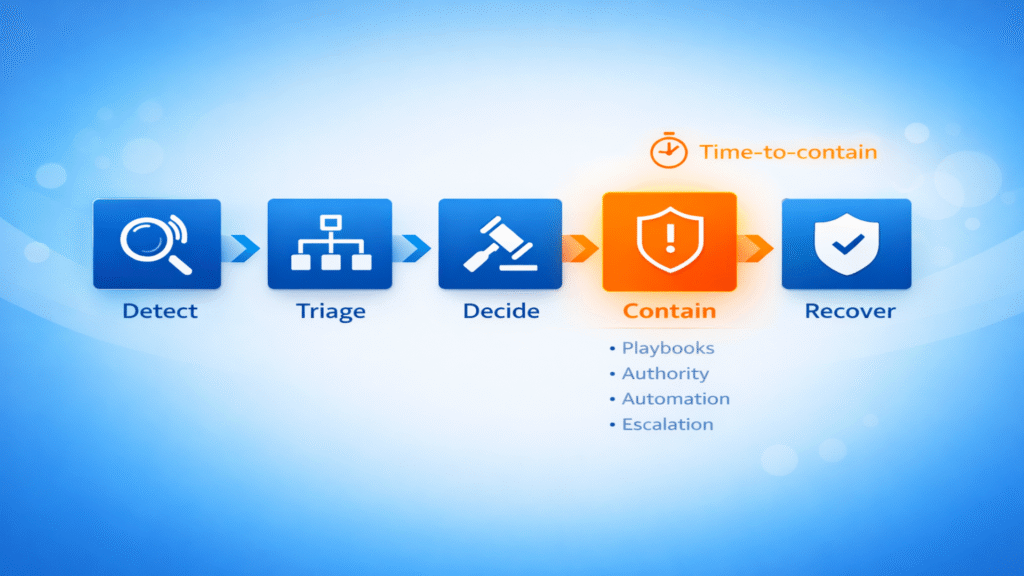
Security detection has improved dramatically over the past five years. Most organization’s now have endpoint detection and response tools, cloud security alerts, identity monitoring, network telemetry, and either a SIEM or a managed SOC. Visibility is rarely the issue anymore. Yet when incidents occur, impact still spreads, because detection alone does not reduce risk. Response does.
In real client environments, the gap between alert and action is where risk grows. We often see alerts generated within minutes, investigation beginning within hours, and containment delayed by uncertainty. That delay is rarely technical. It is operational. Common friction points include unclear authority to isolate devices, no agreed playbooks for specific scenarios, escalation chains that rely on unavailable individuals, and business hesitation about disrupting operations. During that time, attackers move laterally.
Detection without response also creates false confidence. Dashboards look healthy, alert volumes are monitored, and monthly reports show trends. But if response time is slow, dwell time increases, and dwell time is what determines impact. Detection metrics are useful, but response metrics matter more:
• Mean time to contain
• Mean time to eradicate
• Business impact duration
Security maturity is measured by how quickly disruption is limited.
Operational response maturity is practical and designed in advance. It includes:
• Defined playbooks with specific steps for phishing, ransomware, credential abuse, and insider threat
• Pre-approved containment authority with clear thresholds for isolating endpoints or disabling accounts
• Automation where appropriate such as credential resets, session revocation, and device isolation
• Regular simulation through tabletop exercises and scenario testing, because without rehearsal, response remains theoretical
From the BluBiz perspective, in environments we support, the biggest uplift often comes not from adding detection tools, but from refining response workflows. When identity, endpoint, network, and SOC operate in alignment, response accelerates. Speed reduces impact. Clarity reduces hesitation.
A practical next step is to ask your team: if a privileged account is compromised at 11pm tonight, who acts, how quickly, and with what authority? If that answer requires discussion, response maturity needs attention.
