A Backup Is a Copy. Recovery Is the Capability That Matters.
The reassurance thatis not quite a protection. Backup jobs run. Logs show green. Leadership is told the data is safe.
It is a reasonable conclusion, but it is not the same as being protected. Protection is only proven when recovery works in practice. And in most environments, recovery has never been tested against the conditions that actually matter.
Where the strategy quietly breaks down
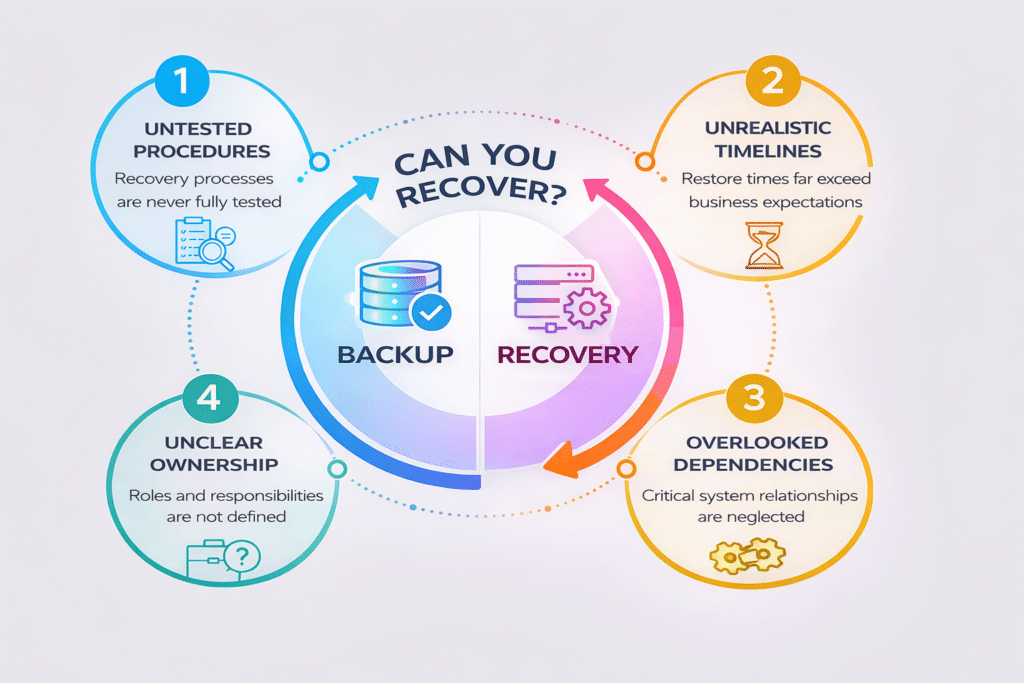
The gap is rarely in technology. Most organisations have adequate tools. The failure points sit elsewhere:
- Recovery procedures live in individual knowledge, not in documented runbooks
- Restore times have never been measured against real business expectations
- System dependencies are assumed rather than mapped
- When an incident occurs, ownership of the recovery process is unclear
Backup is a control. Recovery is a capability. They are not the same thing.
What the board is really asking
When disruption occurs, the conversation moves quickly from infrastructure to impact. How long until we are back? Which services are affected by? Is there a plan?
Leadership does not want confirmation that backups were running. They want confidence that the business can recover within a timeframe it can withstand. That confidence only comes from recovery processes that are tested, documented, and owned.
Making resilience operational
Strengthening recovery readiness rarely requires new investment. The fundamentals are usually enough: defined recovery objectives, documented procedures, mapped dependencies, clear ownership, and a commitment to test end-to-end at least once a year. Simple. Not always easy. But far less costly than discovering the gaps during an incident.
What we consistently find
When we assess disaster recovery environments at BluBiz, the pattern is familiar. Backup jobs look healthy. Infrastructure is sound. But when we trace a recovery scenario end-to-end, the gaps surface quickly.
Procedures are undocumented. Dependencies are incomplete. Recovery times are longer than the business expects. In several environments, addressing these structural gaps alone reduced recovery complexity by up to 40 percent and meaningfully improved confidence across critical systems.
The tools were already in place. What was missing was the structure and the habit of testing.
One question worth sitting with
If a critical system fails today, could your team recover it within the timeframe your business expects, without escalating, improvising, or calling the vendor?
If there is any hesitation, the starting point is not new technology. It is an honest assessment of what you have, what you need, and what stands between the two.
If recovery readiness has not been tested recently, it may be time to assess how well your environment can respond under real conditions.
